2026-02-10 17:12:28 +05:30
# Connecting Google to Rowboat
2026-04-10 00:42:59 +05:30
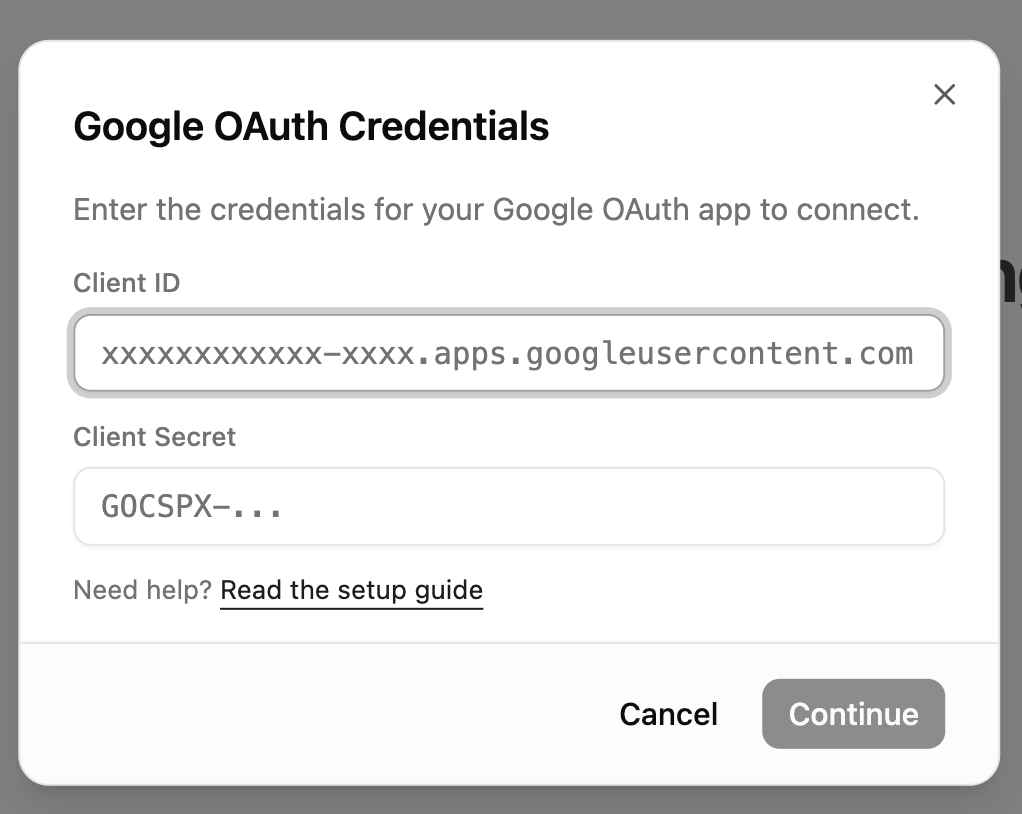
Rowboat requires Google OAuth credentials (Client ID and Client Secret) to connect to Gmail, Calendar, and Drive. Follow the steps below to generate them.
2026-02-10 17:12:28 +05:30
---
## 1️
Go to:
https://console.cloud.google.com/
2026-02-10 17:40:51 +05:30
Make sure you're logged into the Google account you want to use.
2026-02-10 17:12:28 +05:30
---
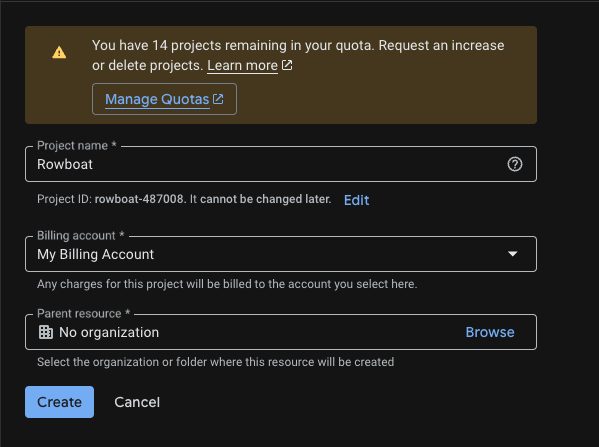
## 2️
Go to:
https://console.cloud.google.com/projectcreate
- Click **Create Project**
- Give it a name (e.g. `Rowboat Integration` )
- Click **Create**
Once created, make sure the new project is selected in the top project dropdown.
2026-02-10 17:40:51 +05:30
2026-02-10 17:12:28 +05:30
---
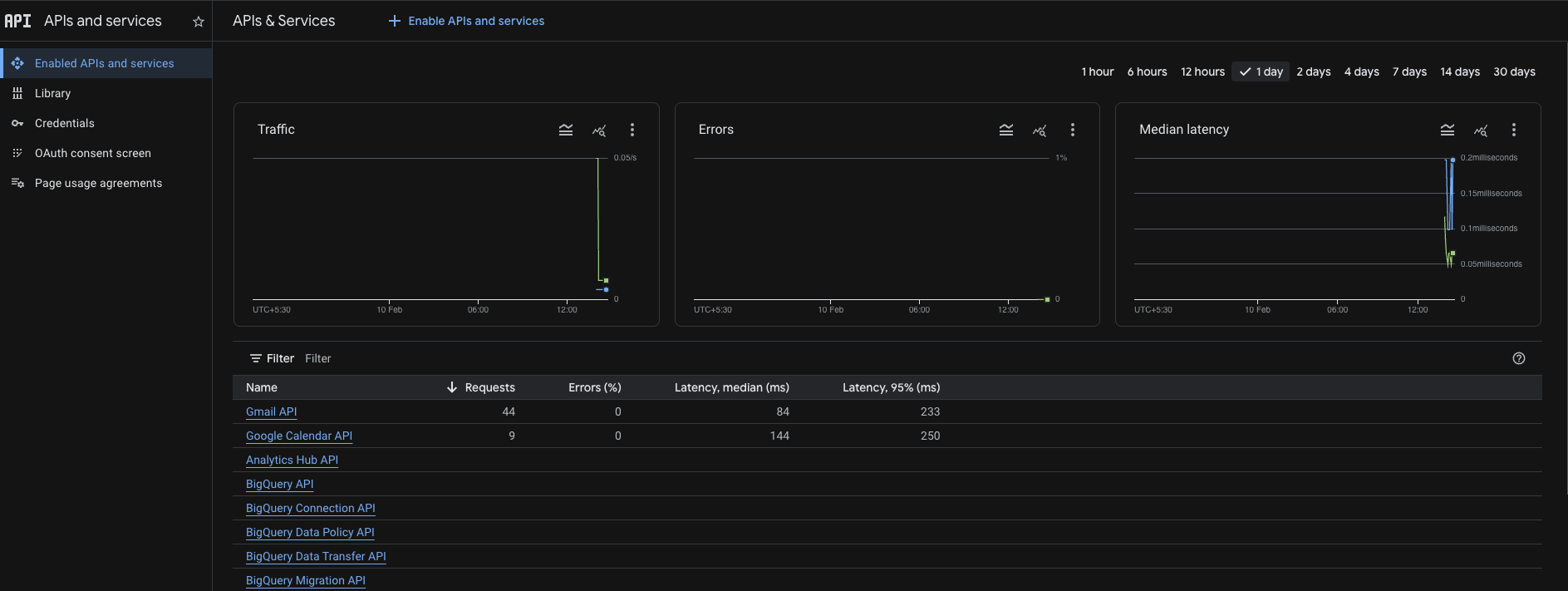
## 3️
Enable the following APIs for your project:
- Gmail API
https://console.cloud.google.com/apis/api/gmail.googleapis.com
- Google Calendar API
https://console.cloud.google.com/apis/api/calendar-json.googleapis.com
- Google Drive API
https://console.cloud.google.com/apis/api/drive.googleapis.com
For each API:
- Click **Enable**
2026-02-10 17:40:51 +05:30
2026-02-10 17:12:28 +05:30
---
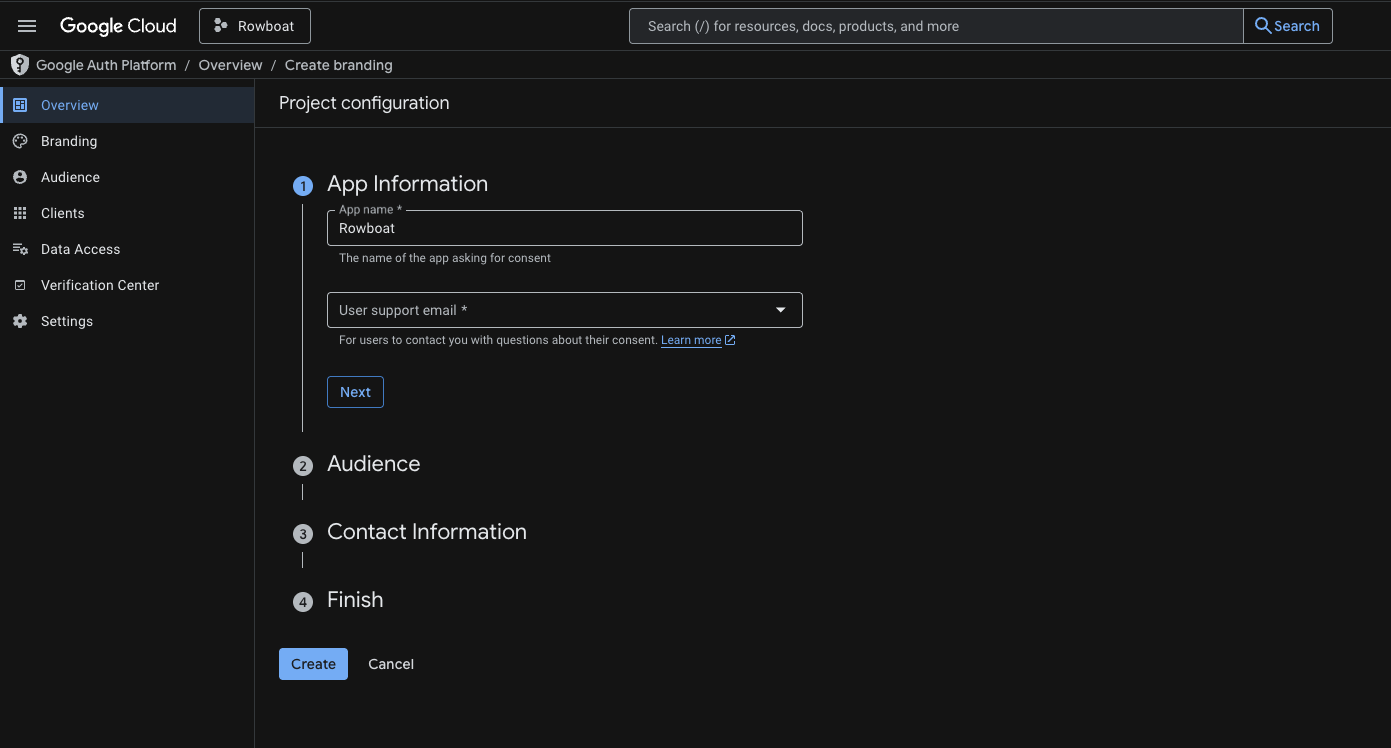
## 4️
Go to:
https://console.cloud.google.com/auth/branding
### App Information
- App name: (e.g. `Rowboat` )
- User support email: Your email
### Audience
- Choose **External**
### Contact Information
- Add your email address
Click **Save and Continue** through the remaining steps.
You do NOT need to publish the app — keeping it in **Testing** mode is fine.
2026-02-10 17:40:51 +05:30
2026-02-10 17:12:28 +05:30
---
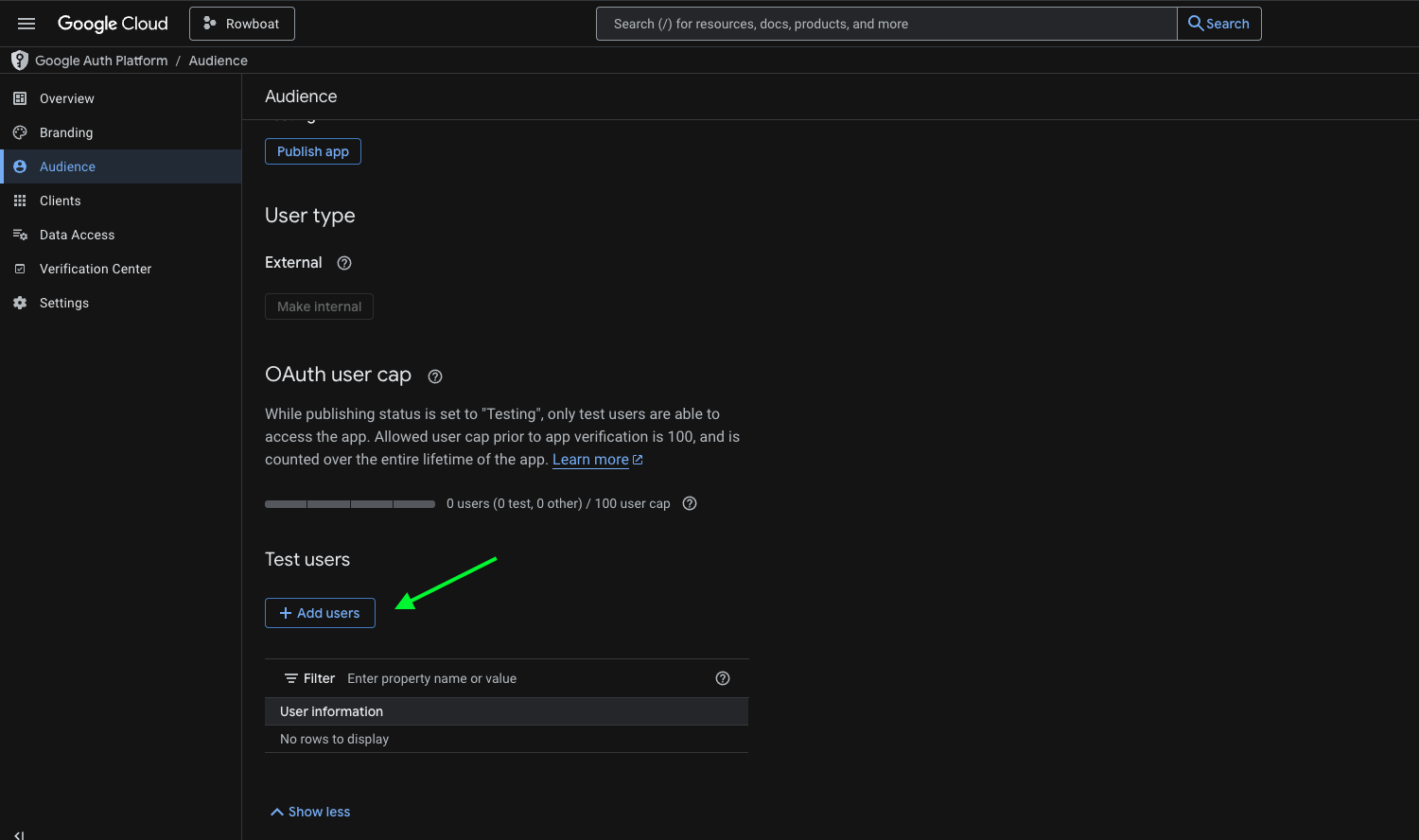
## 5️
If your app is in Testing mode, you must add users manually.
Go to:
https://console.cloud.google.com/auth/audience
Under **Test Users** :
- Click **Add Users**
- Add the email address you plan to connect with Rowboat
Save changes.
2026-02-10 17:40:51 +05:30
2026-02-10 17:12:28 +05:30
---
## 6️
Go to:
https://console.cloud.google.com/auth/clients
Click **Create Credentials → OAuth Client ID**
### Application Type
Select:
2026-04-10 00:42:59 +05:30
**Web application**
2026-02-10 17:12:28 +05:30
- Name it anything (e.g. `Rowboat Desktop` )
2026-04-10 00:42:59 +05:30
### Authorized redirect URIs
2026-04-07 11:24:25 -07:00
2026-04-10 00:42:59 +05:30
Add the following redirect URI:
2026-04-07 11:24:25 -07:00
- `http://localhost:8080/oauth/callback`
2026-04-10 00:42:59 +05:30
Use this exactly: no trailing slash, port **8080** . This must match what the app uses for the OAuth callback.
Click **Create** .
2026-04-07 11:24:25 -07:00
2026-02-10 17:12:28 +05:30
---
2026-04-10 00:42:59 +05:30
## 7️
2026-02-10 17:12:28 +05:30
After creation, Google will show:
- **Client ID**
- **Client Secret**
2026-04-10 00:42:59 +05:30
Copy **both values** and paste them into Rowboat when prompted.
2026-02-10 17:12:28 +05:30
2026-04-10 00:42:59 +05:30
2026-02-10 17:12:28 +05:30
2026-02-10 17:40:51 +05:30
---
2026-04-07 11:24:25 -07:00
## Troubleshooting
**Error after "Authorization Successful"**
If the browser shows "Authorization Successful" but the app then shows an error (e.g. "invalid response encountered" or "response parameter \"iss\" (issuer) missing"):
1. **Check the app logs** (e.g. terminal or dev tools) for the full error. The message there will often indicate the cause (e.g. redirect URI mismatch, missing parameter).
2026-04-10 00:42:59 +05:30
2. **Verify redirect URI in Google Cloud Console** : Open [Credentials → your OAuth 2.0 Client ID ](https://console.cloud.google.com/auth/clients ). Ensure `http://localhost:8080/oauth/callback` is listed under **Authorized redirect URIs** .
3. **Client type** : Make sure you selected **Web application** as the application type. Other types (Desktop, UWP) may not provide a client secret or may handle redirect URIs differently.
2026-04-07 11:24:25 -07:00
---